The High-Trust Trap: Churches Are Easy Targets for Fraud
By design, churches are built on a foundation of faith, compassion, and trust. We are conditioned to act quickly when a brother or sister is in need. While these traits make for a healthy spiritual body, they unfortunately make churches high-trust environments that are prime targets for sophisticated fraudsters.
Scammers know that a staff member is more likely to fulfill a request from their “pastor” than a corporate employee is to follow an unusual order from a distant CEO. To protect your ministry’s resources, it is vital to recognize the patterns of modern church fraud.
Four Common Fraud Tactics
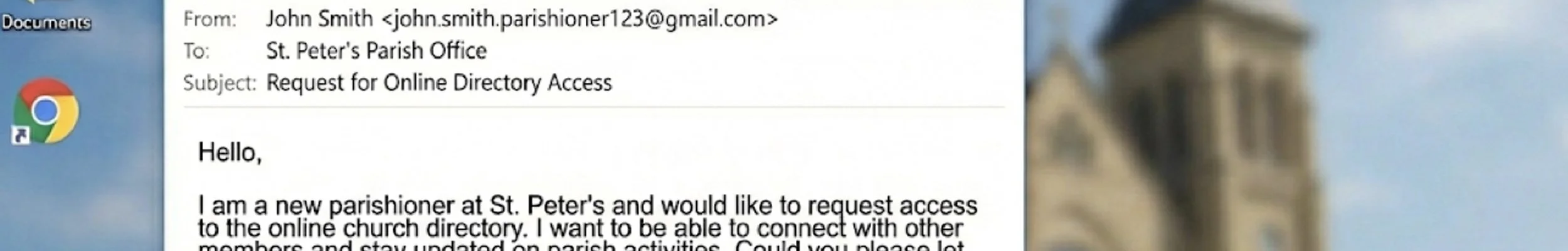
1. The Urgent Database Request
An administrator receives an email that looks like it’s from a trusted leader or a software provider, asking for access to the church’s member directory, or a full export of the church’s member database. The goal? Identity theft. Once a scammer has names, addresses, and giving histories, they can target your congregation individually with even more convincing scams.
2. The Discreet Favor (The Gift Card Scam)
This is a very common tactic. An email — spoofed to look like it’s from the Pastor — arrives saying, “I’m in a meeting and can’t talk, but I need a discreet favor. Can you buy $500 in Google Play or Amazon gift cards for a family in crisis? Just text me the codes.” Remember: A legitimate leader will never ask you to bypass financial internal controls for a “secret” purchase.
3. The Fake Vendor Invoice
Scammers often research who your contractors are. They may send an email claiming to be your landscaper or roofing company, stating they have changed their payment processing and asking you to send your next wire transfer or ACH payment to a new account. They may even construct a legitimate-looking email thread that appears to represent a conversation with another staff member approving an invoice payment. Some scammers also mail a legitimate-looking invoice for renewing your website or email service. Always verify these via a known phone number, in-person conversation, or known website login — never via email link. You won’t receive postal mail invoices for most technology-related services. Those are handled through online billing portals, and are prepaid by credit card.
4. The Employee Payroll Banking Update
We see this nearly every day: an email comes in, appearing to be from a current employee asking for help updating the direct deposit banking information before their next paycheck. Scammers can easily learn who to impersonate from a staff page on your website or LinkedIn listing. Employees should already know that they can make these sorts of changes directly through the payroll provider such as Gusto. If they have trouble signing in, they can use the payroll provider’s forgotten password tools to regain access. There should never be a need to update banking info for someone else, nor to offer guidance on accessing their payroll details beyond redirecting them to sign into their own account at the payroll provider who will have strong practices to prevent fraudulent access or updates.
Stay Vigilant
The best defense is a “Trust, but Verify” policy. Before acting on any financial request — especially those marked “urgent” or “confidential” — pick up the phone and call the person directly. A 30-second phone call can save your church thousands of dollars and hours of heartache.
To help your church protect its mission and its members, use this Church Fraud Prevention Checklist for all staff meetings and volunteer orientations.
Email & Communication Safety
▢ Check the Sender’s Address, Not Just the Name. Scammers can change the “From” name to “Pastor John,” but the actual email address is often a random string of characters or a personal Gmail account created to look like it might be the pastor’s personal email address.
▢ The “Second Channel" Rule. If you receive an urgent request for money, gift cards, or sensitive data via email or text, verify it through a different channel such as calling the person directly on their known phone number, not the phone number they give you in the request.
▢ Identify the “Discreet Favor” Trap. Be skeptical of any request that asks you to keep a purchase confidential or says the sender is in a meeting and can’t talk.
▢ Protect the Database. Never download or email a list of church members or donors unless the request is made through official, pre-approved channels. Make sure you know each person to whom you give database or directory access.
Financial & Vendor Controls
▢ Verify Vendor Changes. If a regular vendor (landscaper, utility provider, etc.) emails saying their banking information has changed, call them at a number you already have on file to confirm before updating your payment system.
▢ Redirect Payroll Banking Changes. If an employee emails saying their banking information has changed, verify that the email is legitimate, and if so, let them know that they can update their information directly via the payroll platform. Guide them to seek help from the payroll platform if they have trouble signing in, who can help them safely and securely access their account.
▢ Dual Signature Policy. Require two people to sign any check over a certain amount, such as $500 or $1,000.
▢ Only Snail Mail for Legal Matters. Government agencies like the IRS or US Marshals will never send a wage garnishment or legal notice via a personal email thread. Official notices arrive by physical, registered mail.
▢ Separation of Duties. The person who records donations in the database should not be the same person who physically deposits the checks at the bank. Separate approving from paying bills.
IT & Data Security
▢ Enable Multi-Factor Authentication (MFA). Ensure all staff email and accounting logins require MFA/2FA with an authenticator app like 1Password, Google Authenticator, or Authy. Temporary codes sent via SMS are less secure, but better than nothing.
▢ Use a Password Manager. Stop the use of the same password across multiple platforms (e.g., the church Facebook page and the church bank account) and use a password manager like 1Password to generate strong unique passwords for every website.
▢ Restrict Admin Access. Volunteers should only have access to the specific data they need for their role. Review access permissions quarterly.
Red Flag Warning Signs
▢ The request creates a sense of urgency.
▢ The grammar, spelling, or tone is off. For example, the sender suddenly sounds very formal or uses phrases they never use.
▢ You are asked to pay via untraceable methods such as gift cards, wire transfers, or cryptocurrency.
If you’re an Auxilio client, talk to your Partner Strategist about how to communicate the signs of fraud to your congregation. If you’re not yet an Auxilio client partner, contact us to learn how we can serve your church or faith-based nonprofit by reducing your administrative burden to free you up for ministry.
Click here for more insights and resources for churches and nonprofits from the Auxilio team.